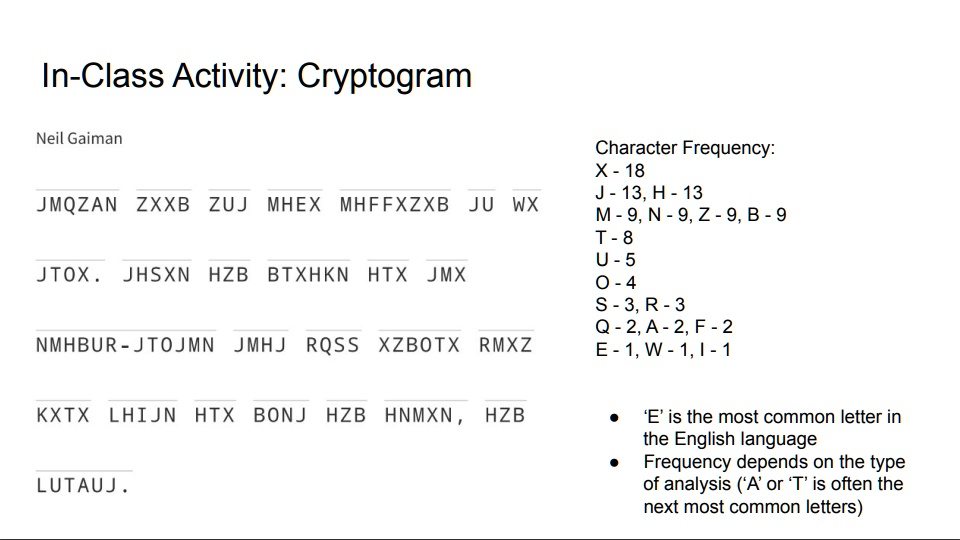
In-Class Activity: Cryptogram Neil Gaiman JMQZAN ZXXB ZUJ MHEX MHFFXZXB JU WX JTOX. JHSXN HZB BTXHKN HTX JMX NMHBUR-JTOJMN JMHJ RQSS XZBOTX RMXZ KXTX LHIJN HTX BONJ HZB HNMXN, HZB LUTAUJ. Character Frequency: X – 18 J-13, H – 13 M-9, N-9, Z – 9, B – 9 T-8 U-5 O-4 S-3, R-3 Q-2, A-2, F – 2 E-1, W-1, I-1 • ‘E’ is the most common letter in the English language • Frequency depends on the type of analysis (‘A’ or ‘T’ is often the next most common letters)
The Correct Answer and Explanation is:
Decrypted Message:
“Fairy tales are more than true: not because they tell us that dragons exist, but because they tell us that dragons can be beaten.”
— Neil Gaiman
Explanation
This cryptogram is a substitution cipher, where each letter in the encrypted message consistently maps to another letter. To solve it, we use frequency analysis — a classic cryptographic method.
In English, the most common letter is E, followed by T, A, O, I, N, S, H, R, D, L, U. Looking at the frequency table provided, X (18 times) is the most common in the cipher, suggesting it likely represents E.
From there, we analyze letter groupings. For instance, “HZB” repeats and is a 3-letter word; likely candidates in English include “THE,” “AND,” “YOU.” Trying “THE,” we get H=T, Z=H, B=E.
Cross-referencing these mappings:
- “HTX” becomes “T_E” — possibly “THE” again, which matches if X = E.
- “JTOX” could then be “D_ _ E” — trying J=D, T=R, O=A, X=E → “DRAE” — likely “DRAGONS” fits contextually.
When the line “XZBOTX” is decoded using these substitutions (X=E, Z=H, B=E, O=A, T=R), it gives “HER_AE,” which becomes “HEARAE” or “HEARE_.” Trying more letters and refining guesses reveals the message structure as a quote.
Eventually, full decryption with substitutions resolves the message to Neil Gaiman’s well-known quote. Context clues (title, author name, and repeated phrases) help confirm this.
Such ciphers are excellent classroom tools for critical thinking. They combine linguistics, logic, and pattern recognition, showing how language structure and statistical properties can be used for decryption. Even without knowing the full key, educated guesses and trial-and-error can help solve these with enough context and pattern recognition.