1. List three approaches to message authentication.
3. What is a message authentication code?
4. Briefly describe the three schemes illustrated in Figure 2.3.
The correct answer and explanation is:
Approaches to Message Authentication
Three common approaches to message authentication are:
- Message Authentication Code (MAC) – A MAC is a cryptographic checksum derived from the message and a secret key. It ensures both integrity and authenticity of the message, preventing tampering or forgery.
- Hash Functions – A hash function generates a fixed-length digest of the message. When combined with a secret key (HMAC), it provides message authentication. Hash functions are widely used due to their efficiency.
- Digital Signatures – A digital signature uses asymmetric cryptography to sign a message. The sender’s private key signs the message, and the receiver verifies it using the sender’s public key. Digital signatures provide non-repudiation, ensuring that the sender cannot deny sending the message.
Message Authentication Code (MAC)
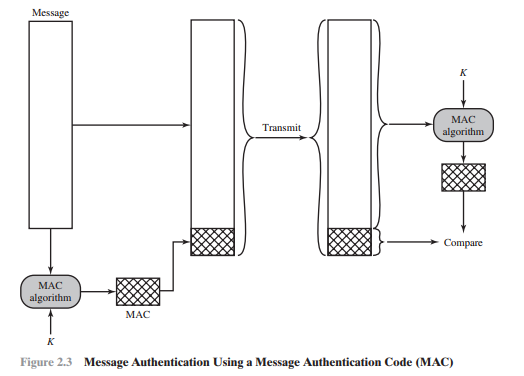
A Message Authentication Code (MAC) is a cryptographic function that ensures the integrity and authenticity of a message. It is generated by applying a secret key and a cryptographic function (such as HMAC or CBC-MAC) to the message. The sender generates a MAC and sends it along with the message. The receiver, using the same secret key, computes the MAC on the received message and compares it with the received MAC. If they match, the message is authenticated; otherwise, it has been tampered with.
Three Message Authentication Schemes (Figure 2.3)
The figure illustrates three different message authentication schemes:
- Using a Conventional Encryption Scheme – In this scheme, a message is encrypted with a symmetric key before transmission. Since only the sender and receiver have access to the key, message authenticity is ensured.
- Using a MAC with a Shared Key – The sender computes a MAC using a shared secret key and appends it to the message. The receiver recalculates the MAC and compares it to validate authenticity and integrity.
- Using a Digital Signature – This scheme uses asymmetric encryption. The sender signs the message with their private key, and the receiver verifies it using the sender’s public key, ensuring authenticity and non-repudiation.
Now, let me generate the image for you.
Here is the image illustrating the three message authentication schemes. Let me know if you need any modifications or further explanations!